How This Chinese APT Hacked the Entire U.S. Telecom Network – And What It Means for National Security
In recent months, a highly sophisticated cyber espionage campaign known as Salt Typhoon has targeted major U.S. telecommunications providers. Linked to Chinese state-sponsored threat actors, this campaign has exposed critical infrastructure and sensitive data through a combination of stolen credentials, advanced malware, and unpatched vulnerabilities. Let’s break down what happened, how it unfolded, and what can be done to prevent such attacks in the future.

How Did the Attack Happen?
The Salt Typhoon campaign relied on a mix of clever tactics and known vulnerabilities to infiltrate telecom networks. Here’s a closer look at the methods used:
1. Credential Theft & Lateral Movement
- Attackers gained initial access by stealing employee credentials.
- Once inside, they used compromised Cisco devices as pivot points to move across the network.
- CVE-2018-0171 (Smart Install Remote Code Execution): Allowed attackers to execute arbitrary code on unpatched Cisco devices.
- CVE-2023-20198 + CVE-2023-20273 (Privileged User Account Creation → Root Command Execution): Attackers used these vulnerabilities to gain privileged access and execute commands with root privileges, taking full control of the system.
- CVE-2024-20399 (NX-OS CLI Command Injection): Improper input validation allowed attackers to execute arbitrary commands as root.
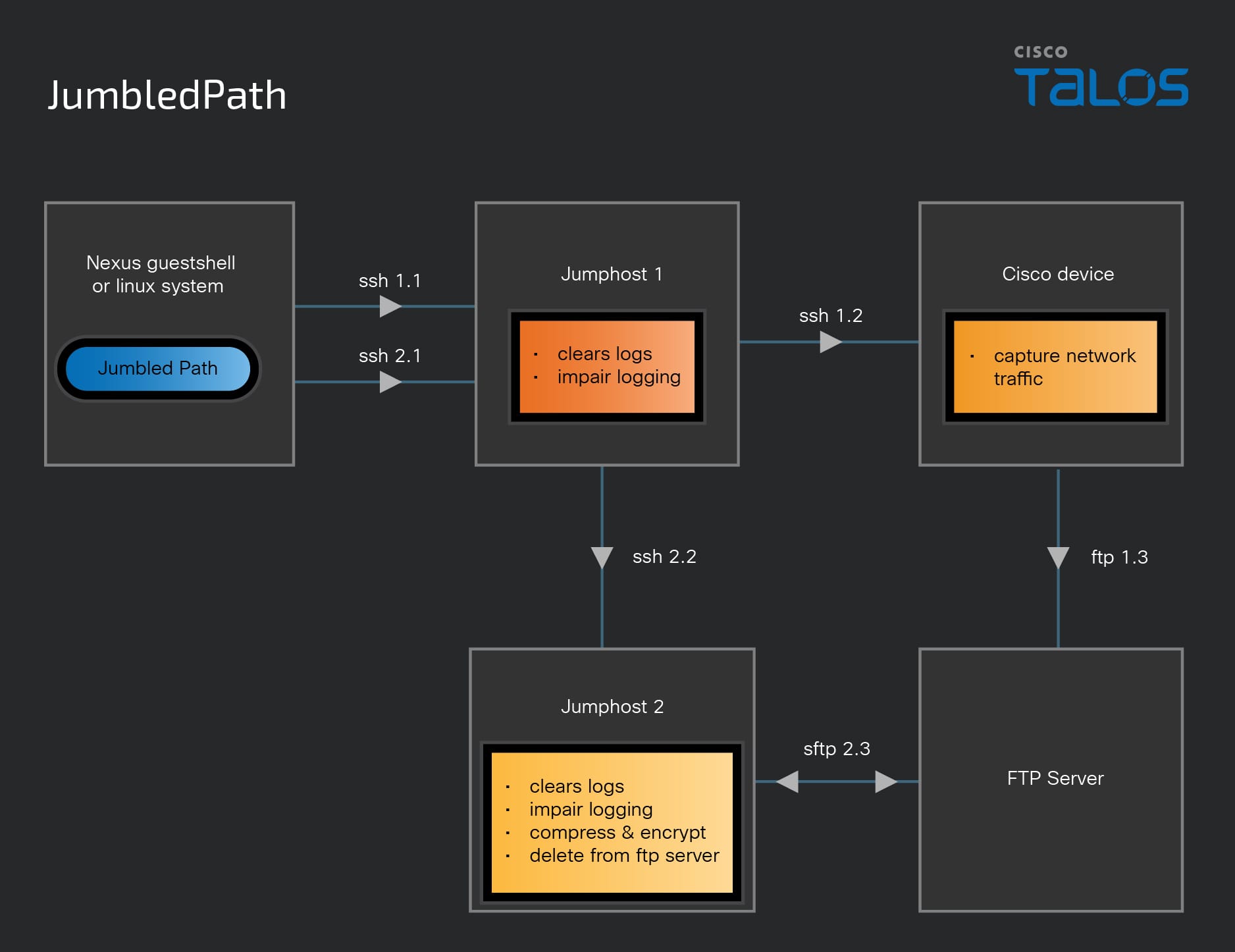
3. Custom Malware – "JumbledPath"
- This malware was deployed to establish persistent remote access on compromised devices.
- It enabled covert communication between infected systems, making detection incredibly difficult.
The Impact of the Attack
The Salt Typhoon campaign had far-reaching consequences, affecting an estimated 1 million users, including key organizations and government entities in Washington D.C. Here’s what was compromised:
- Critical Telecom Infrastructure: Major U.S. telecom providers were infiltrated, raising concerns about espionage and potential disruptions to national security.
- Sensitive Data Exposure: Attackers accessed call metadata, phone numbers, IP addresses, and routing details. This breach also potentially compromised government surveillance operations and high-value targets.
How Can We Prevent Future Attacks?
To safeguard against similar threats, organizations must take proactive steps to secure their networks. Here are some key mitigation strategies:
1. Patch Vulnerabilities Immediately: Apply Cisco’s patches for IOS XE and NX-OS vulnerabilities to close security gaps.
2. Strengthen Access Control: Restrict Web UI access, enforce multi-factor authentication (MFA), and regularly audit user accounts.
3. Implement Network Segmentation: Use zero-trust principles and strict firewall policies to limit lateral movement within the network.
4. Invest in Continuous Monitoring: Deploy SIEM tools, anomaly detection systems, and threat intelligence feeds to identify and respond to suspicious activity in real time.
The Bottom Line
The Salt Typhoon cyberattacks serve as a stark reminder of the vulnerabilities in our critical infrastructure. Without immediate action, telecom networks remain at risk of further state-sponsored espionage. It’s not enough to just patch vulnerabilities—organizations must also invest in advanced threat detection and continuous monitoring to stay ahead of evolving cyber threats.
Learn More:
Videos:
https://www.youtube.com/watch?v=H6U4AtPfY7s
https://www.youtube.com/watch?v=tRATnT577Aw
Good piece.
ReplyDeleteawesome
ReplyDeleteYo
ReplyDelete